Security
Session management
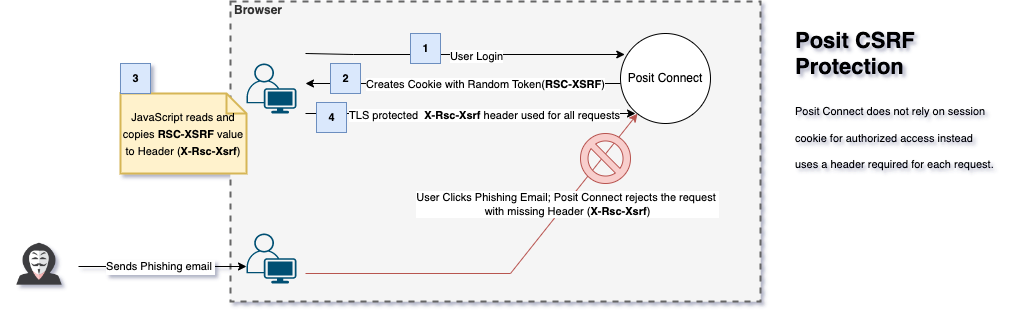
Sessions are stored on the server in Posit Connect. Connect generates a cryptographically secure identifier for each session, which is stored in the rsconnect and rsconnect-legacy cookies. The cookies are HttpOnly by default (ensuring that they cannot be accessed by JavaScript), and use the Secure attribute if Connect is configured to require HTTPS.
When signing into Posit Connect, a browser cookie is used to keep the user logged in. See the Limiting Session Lifetime section for details about the default session lifetime and how to change it.
The server periodically checks the data store for expired cookies and removes them. This happens once per hour by default, but is configurable using the Authentication.CookieSweepDuration configuration setting. This does not affect the lifetime of web sessions, which is controlled by the Authentication.Lifetime configuration setting.
API security
Preventing brute force & dictionary attacks
By default, Posit Connect allows as many login attempts as it can handle from any source when using the PAM, LDAP, and Password authentication providers. Users can log in directly by entering their user name and password.
Setting the Authentication.ChallengeResponseEnabled flag to true enables a CAPTCHA form in the login screen, and requires that CAPTCHA be solved in order to authenticate. Both visual and audio CAPTCHA challenges are provided for accessibility needs.
Hiding Posit Connect server version and build information
By default, Posit Connect sets the Server HTTP header to the Connect version with commit offset, which looks something like Posit Connect v1.2.3-1234. If you would like to hide this information you can configure Server.ServerName to be any string. If you would also like to hide the version and build information within the Connect dashboard you may configure the Server.HideVersion setting to be true.
Browser security
There are a variety of security settings that can be configured in Posit Connect. Some of these settings are enabled by default but can be customized while others are opt-in. Below are some of the security features worth considering.
Web sudo mode
When a user performs a sensitive operation in a web browser (such as creating a new API key), they will be asked to reenter their login credentials. Once the user enters their password properly, their session enters a privileged state internally referred to as web sudo mode which allows them to perform these sensitive operations for a certain window of time without entering their password again. Note that this privileged mode is a notion purely internal to Posit Connect and entirely unrelated to the server’s actual sudo or PAM settings.
This feature is not available on servers configured to use Single Sign-On (SSO) via OAuth2, OpenID, SAML, or proxied authentication.
For all other authentication providers, the WebSudoMode and WebSudoModeDuration configuration options are available within the section pertaining to that provider. If WebSudoMode is set to false, then this protection is disabled. Effectively, all authenticated users are always in privileged mode. WebSudoModeDuration controls the length of time for which a user stays in this privileged mode. From within the section pertaining to your authentication provider (such as [Password], [PAM], or [LDAP]), you can configure:
/etc/rstudio-connect/rstudio-connect.gcfg
; This example is using password authentication. Use PAM or LDAP as appropriate.
[Password]
WebSudoMode = true
WebSudoModeDuration = 10mIn this case, users are prompted for their password before performing sensitive actions, and are then allowed to continue performing sensitive actions for up to 10 minutes without additional prompts. After that point, any sensitive actions require entering their password again.
Regardless of the setting, web sudo mode will never affect calls made outside of a browser using a token or an API key.
Limiting session lifetime
The default Posit Connect configuration enforces the following limits on authenticated sessions:
- Sessions are invalidated after 24 hours, regardless of activity.
- Inactive sessions are considered idle and invalidated after 8 hours.
Once a session is considered invalid, the user needs to reauthenticate before continuing to interact with Posit Connect.
These limits follow good security practices by ensuring that users enter their credentials daily.
The session lifetime and inactive threshold are configurable settings. Adjust the maximum session lifetime by changing the Authentication.Lifetime setting. Session inactivity is controlled with the Authentication.Inactivity setting.
Configure these session settings according to your organization’s security policies.
We use a 24 hour default for Authentication.Lifetime because it means that access is revalidated against your authentication provider (e.g., your Active Directory server) at least once a day. The 8 hour default for Authentication.Inactivity tries to avoid forcing a user to reauthenticate more than once during a typical work day.
Our first configuration example has shorter thresholds than the configured defaults. Users need to reauthenticate after being idle for 30 minutes or after their session lasts for 12 hours. The 30 minute inactivity limit means that sessions may be idle “no longer than a lunch break.”
/etc/rstudio-connect/rstudio-connect.gcfg
[Authentication]
Lifetime = 12h
Inactivity = 30mThis second configuration example has longer thresholds than our configured defaults. Users need to reauthenticate once a week, or after being inactive for a full day. Adopt this type of configuration with care; your organization may want users to reauthenticate more frequently.
/etc/rstudio-connect/rstudio-connect.gcfg
[Authentication]
Lifetime = 7d
Inactivity = 1dPosit Connect uses session cookies to track and enforce both the session lifetime and inactive threshold.
If a user’s session expires or is considered inactive with an application left running in their browser that application’s process is not terminated immediately. Further attempts to interact with the application then cause it to close and then the user will be asked to reenter credentials.
Applications may be able to outlive sessions when opened in Solo mode if their timeout settings are greater than Authentication.Inactivity or Authentication.Lifetime. The settings Scheduler.ConnectionTimeout and Scheduler.ReadTimeout determine the default values for how long a browser running an application can remain idle. By default these are set to 1 hour but individual applications may set higher values independently from the server’s settings.
Guaranteeing HTTPS
If you can guarantee that your server should only ever be accessed over a TLS/SSL connection (HTTPS), then you can consider enabling the HTTPS.Permanent setting. This elevates the security of your server by requiring that future interactions between your users and this server must be encrypted. For more information on using SSL Certificates with Connect, see the Configuring SSL Certificates in Posit Connect section.
Enabling this setting may keep users from being able to access your Posit Connect instance if you later disable HTTPS or if your certificate expires. Use this setting only if you will permanently provide a valid TLS/SSL certificate on this server.
Behind the scenes, this makes two changes:
Introduces HTTP Strict Transport Security (HSTS) by adding a
Strict-Transport-SecurityHTTP header with amax-ageset to 30 days. The default can be overridden by settingHTTPS.StrictTransportSecurityMaxAge. HSTS ensures that your users’ browsers will not trust a service hosted at this location unless it is protected with a trusted TLS/SSL certificate.Enforces the
Secureflag on cookies that are set. This prohibits your users’ browsers from sending their Posit Connect cookies to a server without an HTTPS-secured connection.
Strong HTTPS
You can constrain the TLS version used by HTTPS. This may help you meet the security policy for your organization.
The HTTPS.MinimumTLS setting specifies the minimum TLS version. Clients using a lower TLS version will be rejected. The default minimum TLS version is TLS 1.0. You can configure this setting to 1.0, 1.1, 1.2, or 1.3.
We recommend that you check that the browsers and clients used within your organization are compatible with your minimum TLS version choice. The SSL Labs User Agent List enumerates the TLS capabilities for most popular browsers.
Here is an HTTPS configuration permitting TLS versions 1.2 and above:
/etc/rstudio-connect/rstudio-connect.gcfg
[HTTPS]
Listen = :443
MinimumTLS = 1.2Some Windows builds of the RCurl package are not compatible with TLS 1.1 or TLS 1.2. Windows users should execute options(rsconnect.http = 'curl') to use the local curl binary, if installed, instead of the outdated RCurl package.
Older versions of the RStudio IDE may use webviews that are not compatible with TLS 1.1 or TLS 1.2. In this case, attempting to pair with Posit Connect without TLS 1.0 would open a blank screen instead of a login window. Open the blue link from the pairing window in the browser, or install a newer version of Posit Connect as a workaround.
We recommend using a secure proxy if you need finer control over HTTPS.
TLS cipher suites
Posit Connect uses security best practices around available TLS cipher suites and does not provide configuration options to allow less-secure cipher suites.
Default cipher suites by TLS version
TLS 1.3
TLS 1.3 cipher suites are not configurable and are automatically supported when HTTPS.MaximumTLS is set to 1.3 (the default since Connect v2024.06.0):
TLS_AES_128_GCM_SHA256TLS_AES_256_GCM_SHA384TLS_CHACHA20_POLY1305_SHA256
TLS 1.2 and earlier
For TLS 1.2 and earlier connections, Posit Connect offers cipher suites that provide forward secrecy using Elliptic Curve Diffie-Hellman Ephemeral (ECDHE) key exchange. Starting with Posit Connect v2024.06.0, the following ECDHE-based cipher suites are offered by default:
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHATLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHATLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305_SHA256TLS_ECDHE_RSA_WITH_AES_128_CBC_SHATLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256TLS_ECDHE_RSA_WITH_AES_256_CBC_SHATLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256
The specific cipher suites offered may vary between versions of Posit Connect.
3DES key exchange cipher suites
Starting with Posit Connect v2025.01.0, the following 3DES cipher suites are no longer offered by default:
TLS_RSA_WITH_3DES_EDE_CBC_SHATLS_ECDHE_RSA_WITH_3DES_EDE_CBC_SHA
These cipher suites were removed due to security vulnerabilities in the 3DES algorithm.
RSA key exchange cipher suites
Starting with Posit Connect v2024.06.0, cipher suites using RSA key exchange are no longer offered by default during TLS 1.2 and earlier handshakes. These cipher suites include:
TLS_RSA_WITH_RC4_128_SHATLS_RSA_WITH_3DES_EDE_CBC_SHATLS_RSA_WITH_AES_128_CBC_SHATLS_RSA_WITH_AES_256_CBC_SHATLS_RSA_WITH_AES_128_CBC_SHA256TLS_RSA_WITH_AES_128_GCM_SHA256TLS_RSA_WITH_AES_256_GCM_SHA384
RSA key exchange cipher suites were removed from the defaults because they lack forward secrecy. Forward secrecy ensures that if a server’s private key is compromised, past encrypted communications cannot be retroactively decrypted.
Working with legacy clients
If you have legacy clients that require RSA key exchange or 3DES cipher suites, we strongly recommend using a reverse proxy (such as nginx or HAProxy) in front of Posit Connect. A reverse proxy provides:
- Complete control over cipher suite selection and ordering
- Ability to support legacy clients without compromising Connect’s security posture
- Centralized TLS configuration across multiple services
- Advanced features like OCSP stapling and certificate rotation
See the Using a secure proxy section for guidance on configuring Posit Connect behind a reverse proxy.
If you cannot use a reverse proxy and need support for legacy clients, please contact Posit Support for guidance on available options.
Important: Some temporary workarounds for legacy cipher suites will be removed in future versions of Posit Connect (approximately August 2026). We strongly recommend planning to upgrade legacy clients or implement a reverse proxy solution well before this date.
Customizing cipher suites
Posit Connect does not provide configuration options to explicitly select or order cipher suites. If your organization requires fine-grained control over cipher suite selection, we recommend using a reverse proxy such as nginx, HAProxy, or Apache in front of Posit Connect. This approach provides:
- Complete control over cipher suite selection and ordering
- Ability to support legacy clients without compromising Connect’s security
- Centralized TLS configuration across multiple services
- Advanced features like OCSP stapling and certificate rotation
See the Using a secure proxy section for guidance on configuring Posit Connect behind a reverse proxy.
NGINX
Add the ssl_prefer_server_ciphers and ssl_ciphers directives to your NGINX server block. The following example disables DES, 3DES, IDEA, and RC2 ciphers:
nginx.conf
ssl_prefer_server_ciphers on;
ssl_ciphers -DES:-3DES:-IDEA:-RC2;ssl_prefer_server_ciphers on ensures the server’s cipher preference takes precedence over the client’s. The ssl_ciphers value uses OpenSSL cipher string format. See the OpenSSL ciphers documentation and the NGINX ssl_ciphers reference for the full syntax.
For the complete NGINX proxy configuration, see NGINX reverse proxy.
Apache HTTPD
Add the SSLCipherSuite directive to your Apache VirtualHost block:
httpd.conf
SSLCipherSuite -DES:-3DES:-IDEA:-RC2The SSLCipherSuite directive also uses OpenSSL cipher string format. See the Apache SSLCipherSuite documentation.
For the complete Apache proxy configuration, see Apache reverse proxy.
TLS 1.3
TLS 1.3 uses a separate cipher suite list. The equivalent NGINX configuration is:
nginx.conf
ssl_protocols TLSv1.3;
ssl_ciphers ECDHE-ECDSA-AES256-GCM-SHA384;
ssl_conf_command Ciphersuites TLS_AES_128_GCM_SHA256:TLS_AES_256_GCM_SHA384;
ssl_prefer_server_ciphers off;With TLS 1.3, set ssl_prefer_server_ciphers to off as cipher negotiation works differently.
For more information about Go’s TLS cipher suite implementation and security considerations, see:
You can also configure the minimum TLS version using the HTTPS.MinimumTLS setting. See the Strong HTTPS section for details.
Using a secure proxy
If you would prefer that the Posit Connect process not have access to your TLS/SSL certificates, you may wish to configure a proxy to handle HTTPS requests. To accomplish this:
Ensure that your
Server.Addressis set to the proxy address and uses thehttpsscheme.Set
HTTP.ForceSecuretotrue, which sets theSecureflag on all cookies.Set
HTTP.NoWarningtotrueto suppress the warning regarding running Posit Connect over an unsecured connection, because the connection between the client and the proxy is secured.If necessary, enable the
HTTPRedirect.Listenoption to redirect proxied plain HTTP connections to HTTPS.
Because the connection between the proxy and Posit Connect is not secured in this case, please ensure that the proxy and Posit Connect are connecting on a trusted network where an adversary would not be able to capture plain text credentials. For example, many cloud providers allow isolating servers from the internet while permitting load balancers to access them. Please see your cloud provider’s documentation for more details.
Content sniffing
The Server.ContentTypeSniffing setting can be used to configure HTTP responses with the X-Content-Type-Options header. This header can protect your users from a certain class of malicious uploads.
When Server.ContentTypeSniffing is disabled (the default), the X-Content-Type-Options HTTP header is given the value of nosniff. This instructs browsers not to inspect the content in an attempt to identify its type.
When Server.ContentTypeSniffing is enabled, the X-Content-Type-Options HTTP header is not sent. Browsers are free to analyze the content to detect its type.
Header sanitization
Connect strips the following headers from requests when proxying traffic to subordinate content processes:
X-Rsc-AuthorizationX-Rsc-XsrfAuthorization
Instead of relying on headers to authenticate users to content, you can add them as viewers or collaborators via content Access settings.
Content embedding
The X-Frame-Options HTTP header is used to control what content can be embedded inside other content in a web browser. The relevant attack is commonly referred to as a clickjack attack and involves having your users interact with a sensitive service without their knowledge.
For the purposes of the X-Frame-Options header, Posit Connect distinguishes between “dashboard” and “user” content. The dashboard is any of the internal services or assets that are shipped with Posit Connect. User content is anything uploaded by a user (reports, applications, APIs, etc.)
Server.FrameOptionsContent configures the X-Frame-Options header value for user-uploaded content. By default it is NONE, meaning that the header is not set. This allows user-provided content to be embedded in iframes from any location. If you do not intend for others to embed user content on their sites, you can set this to a value of SAMEORIGIN to ensure that only sites on the same server can embed your users’ content. The Posit Connect dashboard itself uses iframes to present user content in the dashboard, so it is not recommended to set this option to DENY.
Server.FrameOptionsDashboard configures the X-Frame-Options header value for internal services and assets provided with Posit Connect and defaults to a value of DENY. This means that other sites can not embed the Posit Connect dashboard. This setting is more secure in that it protects against clickjacking attacks against the Connect dashboard, but if you plan to embed the dashboard elsewhere you may need to tune this setting.
Some advertised values for this header are not supported across all browsers. Posit Connect does not restrict the values of these headers.
Authenticating embedded content
Connect content can be embedded into other websites via iframe. Connect’s access controls still govern embedded content, and users may need to authenticate if they are not already logged into Connect. In order for this to occur smoothly, both Connect and the embedded content should be configured for redirects back to the original site:
Server.TrustedRedirectsupplies Connect with a list of domains that it is allowed to redirect to after a successful auth attempt. By default, this is empty, meaning no external domains are trusted. You can use this setting multiple times as in the following example:
/etc/rstudio-connect/rstudio-connect.gcfg
[Server]
TrustedRedirect = "https://parent-site.com"
TrustedRedirect = "https://another-site.com"- Any embedded content must include the full redirect URL as a query parameter in the iframe source, using the
framesourceparam. For example:
<iframe src="https://connect-site.com/app?framesource=https://parent-site.com/connectStuff">This gives the authentication mechanism the information needed to return to the initial site after completion.
Cross-Origin Resource Sharing (CORS)
Cross-Origin Resource Sharing (CORS) is a security standard that enables web applications running in one domain to access resources from a server in a different domain. This is particularly important for using Connect’s API from web applications hosted on different domains.
How CORS works
When a web application makes a request to a different domain than where it’s hosted:
- The browser first sends a preflight request (using HTTP OPTIONS) to check if the server allows cross-origin requests
- The server responds with CORS headers indicating what’s allowed:
- Which origins can access the resources
- Which HTTP methods are permitted (GET, POST, etc.)
- Which headers can be included
- Whether credentials (cookies, HTTP authentication) can be sent
Configuring CORS in Connect
Connect’s CORS support is disabled by default. To enable it:
- Set
CORS.Enabled = truein your configuration - Configure allowed origins using
CORS.AllowOrigin - Other CORS headers are pre-configured for common use cases:
Access-Control-Allow-Methodsis set toGET, POST, PUT, PATCH, DELETE, HEADAccess-Control-Allow-Headersis set toOrigin, Content-Length, Content-TypeAccess-Control-Allow-Credentialsis set totrueAccess-Control-Max-Ageis set to 12 hours
For configuration details, see the CORS Configuration section.
Note that CORS uses the scheme, hostname, and port when matching allowed origins. When specifying AllowOrigin values, if the scheme is omitted, http is assumed; if the port is omitted, port 80 is assumed.
Application-level CORS support
In addition to CORS.Enabled = true, you might also need to add CORS handling within your application code, which entails adding OPTIONS as a supported HTTP method. The response to the OPTIONS request must return status code 200 and include the following headers:
"Access-Control-Allow-Origin: *"
"Access-Control-Allow-Methods: DELETE, POST, GET, OPTIONS, PUT, HEAD"
"Access-Control-Allow-Headers: *"Using * allows all domains or headers, respectively. You can narrow the list as required by your organization’s security policies. Below is an example using a Plumber API, but you will need to customize this for your specific code and use case.
plumber.R
#' @filter cors
cors <- function(req, res) {
res$setHeader("Access-Control-Allow-Origin", "*")
if (req$REQUEST_METHOD == "OPTIONS") {
res$setHeader("Access-Control-Allow-Methods","*")
res$setHeader("Access-Control-Allow-Headers", "*")
res$setHeader("Access-Control-Allow-Credentials", "true")
res$status <- 200
return(list())
} else {
plumber::forward()
}
}Custom headers
If you need to include additional HTTP headers that are not covered by any of the above features, you can include your own custom headers on all responses from Posit Connect using the Server.CustomHeader setting.
This feature can be used to accommodate various other security practices that are not explicitly available as options elsewhere in Connect. For instance, X-XSS-Protection, Content Security Policy (CSP), HTTP Public Key Pinning (HPKP), and Cross-origin Resource Sharing (CORS) could all be configured using custom headers.
Custom headers are added to the HTTP response early during request processing. Values may later be overwritten or modified by other header settings. This includes both the security preferences described earlier in this chapter and other headers used internally by Posit Connect or by application or API frameworks such as Flask, Plumber, or Shiny. You should not depend on a custom header that conflicts with a header already in use by Posit Connect.
The Server.CustomHeader takes a value of the header name and its value separated by a colon. Whitespace surrounding the header name and its value are trimmed. You can use this setting multiple times as in the following example:
/etc/rstudio-connect/rstudio-connect.gcfg
[Server]
CustomHeader = "HeaderA: some value"
CustomHeader = "HeaderB: another value"Content Security Policy
A Content Security Policy (CSP) is a security standard that helps prevent cross-site scripting (XSS), clickjacking, and other code injection attacks resulting from execution of malicious content in the trusted web page context. It is a declarative policy that allows server administrators to inform the client about the sources from which the application expects to load resources.
Connect allows an admin to set a CSP by including a CustomHeader value in the server configuration file.
With the following CSP directive, Connect loads and allows user interaction.
/etc/rstudio-connect/rstudio-connect.gcfg
[Server]
CustomHeader = "Content-Security-Policy: script-src 'self'"However, because Connect hosts user-generated content provided by multiple frameworks, the CSP directive above will not work for all content. The following CSP directives allow each supported content type to load and allow user interaction. Replace the recommended <CSP Value> in the CustomHeader directive with the value provided in the table below.
/etc/rstudio-connect/rstudio-connect.gcfg
[Server]
CustomHeader = "Content-Security-Policy: <CSP Value>"| Content Type | <CSP Value> |
|---|---|
| Bokeh App | script-src 'self' 'unsafe-inline' |
| Panel App | script-src 'self' 'unsafe-inline' |
| Jupyter Notebook | script-src 'self' 'unsafe-inline' 'unsafe-eval' https://cdnjs.cloudflare.com |
| Parameterized R Markdown Document | script-src 'self' 'unsafe-inline' data: https://mathjax.rstudio.com |
| Pin | script-src 'self' 'unsafe-inline' |
| Plumber API | script-src 'self' 'unsafe-inline' |
| Python API | script-src 'self' 'unsafe-inline' |
| Python FastAPI | script-src 'self' 'unsafe-inline' |
| Python Shiny App | script-src 'self' 'unsafe-inline' 'unsafe-eval' |
| Quarto Content | script-src 'self' 'unsafe-inline' |
| R Markdown Document | script-src 'self' 'unsafe-inline' data: https://mathjax.rstudio.com |
| Shiny App | script-src 'self' 'unsafe-inline' 'unsafe-eval' |
| Streamlit App | script-src 'self' 'unsafe-inline' 'unsafe-eval' |
| Vetiver API | script-src 'self' 'unsafe-inline' |
| Voilà Dashboard | script-src 'self' 'unsafe-inline' 'unsafe-eval' https://cdnjs.cloudflare.com https://unpkg.com |
The use of 'unsafe-inline' can be replaced with a hash value to tightly restrict the sources of scripts that can be loaded. Here is an example of using a hash value in the CSP directive instead of unsafe-inline:
/etc/rstudio-connect/rstudio-connect.gcfg
[Server]
CustomHeader = "Content-Security-Policy: script-src 'self' 'sha256-gPjlli1HEdLlR0AZTY971/wQVOdSkl9mEinLnxrPpJw='"However, because some frameworks generate scripts dynamically, the use of hashes can lead to a CSP directive that is not sustainable because of the frequently changing hashes. Additionally, if future upgrades of these frameworks change the scripts they use, new hashes will need to be added.
If you plan to host multiple content types on your Connect server, you should modify the CSP to include all of the CSP requirements for each expected content type. For example, if you expected to host both Jupyter Notebooks and R Markdown documents, you would set the CSP directive as follows:
/etc/rstudio-connect/rstudio-connect.gcfg
CustomHeader = "Content-Security-Policy: `script-src 'self' 'unsafe-inline' 'unsafe-eval' https://cdnjs.cloudflare.com data: https://mathjax.rstudio.com`"More information about Content-Security-Policy can be found at:
Application environment variables
User-specified environment variables for applications are encrypted on-disk and in-memory. They are decrypted only when a process is about to be started.
Network security
When Posit Connect is running in High Availability mode or off-host execution mode there are a few important aspects to consider when securing your network. Administrators must have a good understanding of their network topology when evaluating whether additional configuration is required to meet their organization’s security and compliance standards.
Database communication
If Connect is configured to use a Postgres database to store state, you may need to enable SSL for all database connections. This can be accomplished by setting the sslmode= parameter to the desired value in the Connect Postgres.URL configuration.
Filesystem communication
If Connect is configured to use a network filesystem to share state between nodes, depending on your organizational policy and network topology, it may be necessary to configure encryption for data-in-transit when accessing the network filesystem from each Connect node. The steps to accomplish this vary by filesystem provider so we do not cover the setup here.
Content process communication
Connect communicates with the running content process (the interactive R or Python application) using HTTP/HTTPS. Additionally, some communication occurs over websockets (Shiny apps, for example). Connect also communicates with the content session itself via ping and metrics endpoints.
When the config option Applications.ContentSessionTLS is enabled, these communication channels are encrypted using self-signed certificates via HTTPS/TLS. Connect will proxy content process communications through the session process, which receives TLS certificates via encrypted environment variables from Connect. The content session process establishes TLS communication with Connect and subsequently terminates TLS before proxying traffic to the running content process over localhost.
The TLS certificates used by the session process to encrypt communications are signed by an ephemeral root CA which is created by Connect at startup and is not persisted or exposed outside of process memory.
The TLS certificates themselves also are not persisted or exposed outside of process memory except via the encrypted environment variables mentioned above. They only exist during the lifetime of the content process. Each content process uses a unique certificate.
This feature can be disabled by setting the config option Applications.ContentSessionTLS to false, but be aware that this means that traffic between the Connect and content pods in off-host execution will traverse an unencrypted network boundary. In this case we recommend using a service mesh to secure network communication as described in the next section.
Service mesh
When Posit Connect and its supporting infrastructure (NFS and Postgres) are running inside of a Kubernetes cluster the network traffic can be encrypted transparently by installing a service mesh within the cluster. The service mesh will encrypt all pod-to-pod L4 network communication within the Kubernetes cluster. This ensures that each of the 3 communication channels described above will be encrypted by default, with no additional configuration.
Cilium and Istio are popular service mesh options that can be used to enable secure end-to-end encryption by default for your Connect installation.